 |
Saturday, February 21, 2004 |
 Have you had your laptop long enough to wish you'd known how to extend the life of it's battery?
Have you had your laptop long enough to wish you'd known how to extend the life of it's battery?
You will when you go to purchase a replacement. I spent nearly $150 for my latest laptop battery replacement.
 And, what about the new batteries? What's different about a Lithium-Ion (Li-Ion) battery?
And, what about the new batteries? What's different about a Lithium-Ion (Li-Ion) battery?
Do I treat it the same as I did the first Nickel-Cadmium rechargable batteries? The answer is: No.
Lithium-Ion Batteries Have No "Memory"
The main thing to know about these new Lithium-Ion rechargeable batteries is this: they have no "memory" like Nickel-Cadmium (NiCad) and Nickel Metal Hydride (NiMH) batteries do.
 What this means is that you don't need to make sure the battery is fully drained before charging it up again. With NiCad and NiMH batteries the effective life of the battery is reduced considerably because of this "memory" effect. Not so with Li-Ion.
What this means is that you don't need to make sure the battery is fully drained before charging it up again. With NiCad and NiMH batteries the effective life of the battery is reduced considerably because of this "memory" effect. Not so with Li-Ion.
With your Lithium-Ion battery feel free to charge it any time, no matter how discharged it is. Charging the battery while it still has quite a bit of charge makes absolutely no difference to the overall life of the battery.
However, your computer's "fuel guage" may eventually get a bit innacurate without a complete discharge. Read on for details.
"Fuel Guage" Accuracy
It's recommended that every 30 charges or so that you completely discharge the battery so that the "fuel guage" can recalibrate itself. If you don't, your computer may eventually say that the battery is empty when in fact it's half full, for example. When this happens the computer could actually operate for a longer period of time than it thinks it can.
Doing a complete discharge followed by a full recharge will keep the gauge accurate.
Li-Ion Battery Life Span
The other thing to know about Li-Ion batteries is that the newer they are the better they are. Their ability to hold a charge diminishes every day, starting the day they're manufactured. Li-Ion batteries' effective life span is around 2-3 years.
Avoid purchasing spare lithium-ion batteries for later use. Observe manufacturing date. Do not buy old stock, even if sold at clearance prices.
Keep 'Em Cool, Store At a 40% Charge
A Li-Ion Battery's useful life diminishes considerably if it's subjected to high heat, and oddly enough if the battery is left fully charged for long periods of time.
If you take advantage of your laptop-enabled mobility, as I am, you want ready access to a full battery when you're out and about, so we're stuck with that aspect of our Li-Ion's deterioration. But if you don't plan to use your Li-Ion battery for a while, don't leave it fully charged. It's life will be extended if you first bring the charge level down to around 40%. (Also note that it's best not to leave a Li-Ion battery fully discharged. Short term is fine, long term: 40% is best.)
Li-Ion Phone Battery?
 If you happen to have a Li-Ion battery for your mobile phone: watever you do, don't leave the battery sitting on the dash of your car in the hot sun! That'll reduce it's life big-time.
If you happen to have a Li-Ion battery for your mobile phone: watever you do, don't leave the battery sitting on the dash of your car in the hot sun! That'll reduce it's life big-time.
Quote ("Avoid purchasing ... clearance prices.") and Reference: Isidor Buchmann's web site, batteryuniversity.com. Mr. Buchmann is the founder and CEO of Cadex Electronics Inc., in Vancouver BC.
Laptop & laptop batteries images found at: Apple
"Li-Ion" Batteries image source: LG Chem
Phone battery found at: Amazon
|
|
 |
Sunday, February 1, 2004 |
To remove the My Doom virus immediately, proceed to Step 1 and 2, below.
MyDoom.B Mischief
 The new version of the My Doom virus contains minimal technical innovations over it's predecessor (My Doom.A). MyDoom.B propogates itself via email and the KaZaA file-sharing network just as the "A" version did. One main difference is the email it sends out contains a different set of text strings in the body. The carrier file is about 28 KB in size and contains the text string: "sync-1.01", "andy", "I'm just doing my job", "nothing personal", and "sorry".
The new version of the My Doom virus contains minimal technical innovations over it's predecessor (My Doom.A). MyDoom.B propogates itself via email and the KaZaA file-sharing network just as the "A" version did. One main difference is the email it sends out contains a different set of text strings in the body. The carrier file is about 28 KB in size and contains the text string: "sync-1.01", "andy", "I'm just doing my job", "nothing personal", and "sorry".
MyDoom.B is scheduled to launch attacks on www.sco.com and www.microsoft.com between February 1 and February 12, 2004.
The worm also modifies the operating system to prevent users from reaching many anti-virus vendors' sites, security-related news sites and various sections of the Microsoft site, as well as downloading data from banner networks.
Step 1: Run Kaspersky's CLRAV Remover
Download Kaspersky's CLRAV Remover here, close all active applications, and run it. After running the remover you'll restart your computer.
CLRAV scans the computer memory and hard drive of the infected machine, neutralizes the worm and restores the original configuration of the Windows system registry.
Additionally, this removal tool copes effectively with other malicious programs, including Klez, Lentin, Opasoft, Tanatos, Welchia, Sobif, Dumaru and Swen. Given the current outbreak, CLRAV is most useful for users, who have installed anti-virus protection that does not detect and delete Mydoom correctly.
Step 2: Do a Virus Check
If you don't have any anti-virus software, take a look at the links below. Get yourself setup with some anti-virus software and do a virus check.
See also:
Computer Associates; http://www3.ca.com/virusinfo/virus.aspx?ID=38114
Microsoft: https://information.microsoft.com/security/antivirus/mydoom.asp
Sophos: http://www.sophos.com/virusinfo/analyses/w32mydoomb.html
Symantec: http://securityresponse.symantec.com/avcenter/venc/data/[email protected]
US CERT Technical Alert TA04-028A; http://www.us-cert.gov/cas/techalerts/TA04-028A.html
Source: Virus Encyclopedia
Image source: CNN
|
|
 |
Wednesday, August 27, 2003 |
Have you ever wanted to get rid of the date-stamp your camera puts on your photos? Put Photoshop's Rubber Stamp Tool to use and you can make stuff vanish -- like magic!
How's It Done?
 Touching-up your photos in Photoshop is easier than you might think. The only tool used to manipulate the images you see here was the Rubber Stamp Tool (Photoshop 5.5 "Rubber Stamp Tool" icon shown to right, other versions may vary).
Touching-up your photos in Photoshop is easier than you might think. The only tool used to manipulate the images you see here was the Rubber Stamp Tool (Photoshop 5.5 "Rubber Stamp Tool" icon shown to right, other versions may vary).
In Photoshop, simply click on the Rubber Stamp Tool, then hold the Alt key (PC) or Option key (Mac) down while you click the mouse on the location you'd like to "pull" texture from. Once the "source" spot has been specified you can then click the mouse (without any keys held down) on the "destination" spot that you'd like to change.
To get good results you'll want to pick "source" spots with textures that will fit-in with the "destination" area.
That's all there is to it! Practice the process a bit and you'll soon be a "Photo Magician"!
Now You See It...
Notice my Dad's fingers above my Grandfather's head on this one:
Now You Don't!
... the final result:

If this tip worked for you, I'd love to hear it! Click the envelope icon (above, in the right portion of this page) to send me a quick message.
- Kevin JT
|
|
 |
Thursday, August 14, 2003 |
 The best way to maintain domain name ownership (and thus keep others from snapping your name up upon expiration) is this:
The best way to maintain domain name ownership (and thus keep others from snapping your name up upon expiration) is this:
If you're intent on keeping a domain name, be sure to renew it well-before the expiration date.
I suggest renewal a month or two in advance of the expiration date. This will give you time to attend to anything unexpected.
Around renewal time I find that I often end up transferring my domain names to better, lower-priced registrars, which adds a little time. See domains.zaz.com for the lowest prices I've been able to find.
Domain Ownership
Once you've successfully registered a domain name you own it. But your ownership only lasts as long as it's registered in your name. That is, once it expires you no longer "own it". Read on to understand exactly what happens when and if your domain does expire.
The Expiration Date
As indicated above, renewal of your domain name should be done a month or two before the expiration date. If you find you're in a crunch, and the expiration date is only 7 to 10 days or so away it is still possible to renew your name, you'll just want to be sure everything goes smoothly.
If the expiration date is still approaching the first order of business is to make payment to your existing registrar. Get payment to them on or prior to the expiration date. If you'd like to transfer your domain to a better or less expensive registrar and there's time, it is possible, though somewhat risky (the closer you are to the expiration date). If you have the assistance of someone who's done it before successful transfer and renewal can be consummated if initiated around 7 to 10 days prior to expiration.
It Expired, But I Want to Keep It!
If the domain you'd registered has already expired and it's still 30 to 35 days from the expiry date you're within the Grace Period. During this time the status of your domain will likely be set to "Registrar-Hold". Try renewing the domain with your existing registrar. Do so immediately, as it get's rather expensive to re-acquire the name if you let it slip into the "Redemption Period" (see details on this below).
Costly Redemption Period
If the expiration date was more than 30 or so days ago, but it's still been less than two-and-a-half months or so (approximately 65-70 days), your domain has likely slipped into the Redemption Period.
At this point you no longer own the domain name, but you can still get it back, for a price. It'll likely cost you somewhere between $80 to $350 to get the name back during the Redemption Period. If the name represents significant value to you it is advisable to go ahead and re-acquire the name during this period. Once the redemption period is over your name will be available for registration by anyone.
Back-Ordering
If the name in question has little value, or the domain name was last owned by someone else there are two other viable options:
- Back-order the name. (See details on how to do this below.)
- Chance it and register the name later once the domain is out of the redemption period. NOTE: This option is not advisable since it is quite possible that someone else has back-ordered the domain, especially if it appears to have some value.
There are numerous services that allow you to backorder domain names. What they do is monitor the domain name until it becomes available. When it becomes available the name is registered on your behalf. There is no guarantee that you'll get the name, since others may also be backordering the same name. If someone else had been the owner there's also a chance that they'll actually pay to retain ownership.
I've seen costs in the range of $35 to $60 and up for this service. The best price I could find for back-ordering can be found here: backorder.zaz.com (Back-ordering here costs less than $20, and if you don't get the domain name you can plug another name into the system. Do so within 2 weeks after the previous name became unavailable to keep the backorder credit. The credit to the back-order system is valid for 1 year.)
If you have other questions, or need help with your domain name(s), feel free to call Kevin JT Binder toll-free at 1-877-3-BINDER (1-877-324-6337), or visit netcoach.us
".com" image source: ABC News
|
|
 |
Wednesday, August 13, 2003 |
3 Easy Steps to Eliminate the Windows DCOM Security Vulnerability.
If you know your computer has the "blaster" worm virus, skip ahead to "Eradication".
"Blaster" News
 According to cnet, the MSBlast (aka "Blaster") worm infected as many as 100,000 Windows computers in just 24 hours. Infection appears to be slowing due to poor programming of the worm. However, whether you have it or not, you'd best eliminate the possibility of infection to your Windows operating system by eliminating the widely publicized "DCOM" security vulnerability (variations of the "blaster" worm could eventually infect your Windows system if you don't). If your system is worm free, keep it that way by following the 3 steps listed below under "Protecting Against Infection".
According to cnet, the MSBlast (aka "Blaster") worm infected as many as 100,000 Windows computers in just 24 hours. Infection appears to be slowing due to poor programming of the worm. However, whether you have it or not, you'd best eliminate the possibility of infection to your Windows operating system by eliminating the widely publicized "DCOM" security vulnerability (variations of the "blaster" worm could eventually infect your Windows system if you don't). If your system is worm free, keep it that way by following the 3 steps listed below under "Protecting Against Infection".
The DCOM security vulnerability was published on the Microsoft web site on July 16, 2003. It was only a matter of time before the malicious-minded would flaunt the vulnerability. That day came yesterday.
The worm crashes (or "restarts") some systems because it incorrectly tries using a Windows-2000-specific exploitation technique on Windows XP systems, and vice versa. Whether or not your system is behaving oddly, you can easily detect whether your system has the Microsoft (MS) Blast (or "blaster") worm by following the 3 steps below.
Detection
It's very easy to detect whether you're infected by the MSBlaster worm. Simply follow these 3 steps:
- Press control-alt-delete, then click on "Task Manager"
- Select the "Processes" tab, then click on the "Image Name" column to sort alphabetically
- If there is a process named "msblast.exe" running, then it has been infected
If your system is infected, skip ahead to "Eradication".
Protecting Against Infection
To eliminate the DCOM security vulnerability and protect your system against infection by the MSBlast worm (or any "blaster" variations), follow these 3 steps:
- Login to Windows with administrator rights.
- Start Internet Explorer and direct the browser to windowsupdate.microsoft.com
- Follow the instructions. Install any necessary updates, paying special attention to those in the "Critical Updates and Service Packs" section.
Eradication
Eradication of the worm is relatively easy once detected. Follow these steps:

- Login to Windows with administrator rights.
- Start Internet Explorer and direct the browser to windowsupdate.microsoft.com
- Follow the instructions. Install any necessary updates, paying special attention to those in the "Critical Updates and Service Packs" section.
- Reboot the system. Log back in with Administrator rights.
- Press control-alt-delete, then click on "Task Manager"
- Select the "Processes" tab, then click on the "Image Name" column to sort alphabetically
- Find the process named "msblast.exe", and click it once, then press "End Process"
- Use Windows Explorer to navigate to the "system32" directory (found in the "winnt" directory on Windows 2000 machines, and in the "windows" directory on Windows XP computers).
- Locate the "msblast.exe" file inside the "system32" directory and delete it.
- Reboot the system.
That'll do it!
Registry Entry Elimination (Optional)
Though not necessary, purists can also take the following steps to eliminate a registry entry that's already been disabled by deletion of the "msblast.exe" file, above. Be very careful, however, as any mistaken change to the registry could render your system inoperable. Very carefully take these steps:
- Start the registry editor by clicking the "Start" button, then "Run..." and typing "regedit".
- In regedit navigate to the following "key": HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- In the right section of the registry editor find:
"windows auto update"="msblast.exe"
and delete it.
- Reboot the system.
You've successfully eliminated the MSBlast worm!
Read the cnet article (referenced at top) here.
The top-most "worm" graphic was found here.
"Worms Blast" is a game by Raveware. The logo was found here.
|
|
 |
Saturday, July 12, 2003 |
To stop the Windows Messenger Service pop-up spam immediately skip ahead to "4 Steps to Stopping Messenger Service".
You'll find "Thank You's and Testimonials" listed at the end of this post.
My Experience: 5+ Months of Windows Pop-Up Spam
 I can't believe that for the past five and a half months I've allowed Messenger Service Pop-Up Spam to show up on my Windows 2000 Server. I'd kept simply hitting the close-box of each Messenger Service message that showed up.
I can't believe that for the past five and a half months I've allowed Messenger Service Pop-Up Spam to show up on my Windows 2000 Server. I'd kept simply hitting the close-box of each Messenger Service message that showed up.
It wasn't until today that I decided to do a quick Internet search to learn more about this rude spam mechanism that I kept thinking Microsoft would put a stop to with a patch or an update.
"Feature" vs. Security Vulnerability
Microsoft apparently has seen Messenger Service as a Windows "feature" ever since it was first introduced in Windows NT 3.5.
In actuality, the Windows Messenger Service is a security vulnerability, it allows spam direct access to your NT based Windows OS.
Vulnerability: Windows NT, Windows 2000, Windows XP
 Windows XP users are susceptible to Messenger Service spam (as I am on Windows 2000), since XP is based on NT, but Windows 95, 98, and Me users are not (they're not based on NT).
Windows XP users are susceptible to Messenger Service spam (as I am on Windows 2000), since XP is based on NT, but Windows 95, 98, and Me users are not (they're not based on NT).
Stopping the Pop-Ups
Stopping the Windows Messenger Service Pop-Ups is really very easy. You can stop the service now by following the "4 Steps to Stopping Messenger Service", below.
I'd suggest first sending yourself a message with the service so that when you stop it you can again try sending a message and see that it doesn't get through. Here's how to do that:
 Sending Yourself a Message with Messenger Service:
Sending Yourself a Message with Messenger Service:
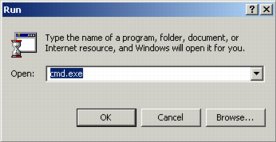
- From the start menu select "Run..."
- Type "cmd.exe", then click "OK"
- Type "net send 127.0.0.1 hi" (as shown below)
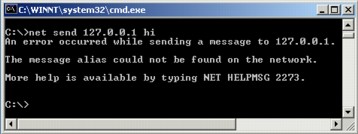
If cmd.exe responds with "the message was successfully sent to 127.0.0.1", as below, your system is vulnerable to pop-up spam. You should take the "4 Steps to Stopping Messenger Service", further down.

Once you've disabled and stopped Messenger Service (if you haven't yet, go ahead and do it now then come back to this), sending yourself a message, as described above should result in the following response from cmd.exe: "An error occurred while sending a message to 127.0.0.1.", like so:
4 Steps to Stopping Messenger Service
- Go to the "Start" menu, choose "Run", type in "services.msc", then Click "OK".
- Scroll (down) to "Messenger", select it, right-click it and choose "Properties".
- Next to "Startup type:" choose "Disabled", then click the "Stop" button.
- When stopped, click "OK".
Verifying that Windows Messenger Service is Disabled
I highly recommed verifying that Messenger Service is disabled, as indicated further above, under "Sending Yourself a Message with Messenger Service". This way you get the immediate gratification of seeing that Windows Messenger Service pop-up spam has been stopped.
If this FAQ has been helpful I'd love to know. Send me a quick message by clicking on the  email icon. Want to help some others? Send them this URL: popup.zaz.com (simply type this into any web browser to get this page). email icon. Want to help some others? Send them this URL: popup.zaz.com (simply type this into any web browser to get this page).
- Kevin JT Binder, 1-877-3-BINDER
www.computercoach.us
Spam image source: Dan Garcia's Spam page
Thank You's and Testimonials
|
I just started getting those pop ups a month ago. I typed in "messenger service pop up" on google and found your site. I can't believe how simple your instructions were to fix that annoying problem! I've sent your link to several friends, and will continue to do so!
|
Thank you so much for the info. I have been trying to stop those pop us for months. They kept giving my www addresses, but when I got there they wanted 24.95 or more for their programs like fightPopups, bustpopups, and defeast messenger. What a joke. Great to know there are still humans out there. Now I have to just get rid of the junk mail and keep myself virus free.
Thank you again,
- Roxanne
|
Thanks a lot. It worked great.
- 6 Speed Jetta Tim
|
Thanks for the details on how to stop Windows Messenger pop up spam. It worked like a charm.
- Kaylene
|
[Messenger Service] OBITUARY: August 16, 2003
The Death of Messenger Service was reported today at 10:30 AM. Messenger Service [MS] had been residing at 8200 Dell for the past 3 months but it's origins are still unknown. MS belonged to a subversive group known as SPAM. MS held the rank (and I do mean RANK) of "Chief-Pain-In-The A--." MS is survived by members of the Pop-Up family whose numbers are dwindling due to the in(ter)jection of "Binder [Inoculator]" which is attributed to the death of MS. There will be no Services...no more no more no more no more. In lieu of flowers send notes of thanks to Institute of Kev.
xoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxoxox
I cannot thank you enough but those are hugs and kisses on the above line. For this old duffer, your instructions were easy to understand and to implement. I got to the point where I was ready to rip out my computer and beat it with a rolling-pin! but thanks to you I have managed my anger and channeled it to a more deserving recipient...George Bush ;O)
- Mary
|
Thank you so much for the information on stopping those very annoying messenger pop ups. I followed your instructions and it worked like a charm. I can now browse in peace!!!
- TW
|
Kevin,
Thanks so much for your article on How-To Stop Windows Messenger Service Pop-Up Spam. They've been driving me crazy for weeks now with ads offering me a way to purchase software that will make it stop. Your free advice did the trick.
Thanks for the integrity.
Paula
|
Hey! Thanks for your tips! I felt really pissed that someone was spamming me through my computer. Being in the computer industry (programming part) I felt helpless against these intrusions! Your helpful website came up right away on google and I am SO thankful!
Keep up the great work!
- Michelle
|
Thank you so much for telling how to turn off the messenger popups.
- Ronald
|
Hi,
Just wanted to say thanks for the popup spam killer tip. I'm real glad to get rid of the messages :-)
Thanks
NS
|
Thank you for the key to ending messenger service!! So many of them are actually selling programs to stop their own messages!!
Thank you!
- C
|
THANK YOU for posting info on disabling the messenger service. It was getting maddening, to the point where I couldn't keep reading because they were popping up so often. I was afraid I was going to through my laptop through the window. I am so happy for this info, there was no way I was going to pay those people to stop them!
Thanks,
Amy
|
|
|
 |
Friday, June 13, 2003 |
A domain name is the "main" part of a web address. It's the "anything.com" in "http://www.anything.com".
The domain name for my business is "zazcorp.com", whereas my personal domain names are "kevinbinder.com" and "kevinbinder.net". (Why both ".com" and ".net"? Read on for more on that below.)
What's a Sub-Domain?
We often type "www" and a dot before domain names. The "www" portion is called a sub-domain. For example, I've set up "about" as a sub-domain to "kevinbinder.com". To read about me, you'd go to "about.kevinbinder.com".
"kevinbinder.com" is the domain name. "about" is the sub-domain.
What's a URL?
URL stands for Uniform Resource Locator (apparently not "Universal Resource Locator" as I've often thought).
URLs often start with "http://", but they can also start with "ftp://", etc. All the URLs I've ever seen have a colen-slash-slash in them ("://"). Sometimes the http has an "s" in it as in "https://" which tells your web browser and the server your connected to encrypt everything, thus making it "secure".
URL vs. Domain Name
What's the difference between a domain name and a URL?
A URL is an entire web address, wheres a domain name is what I'd call it's "root" — the main part of the address.
When visiting a web site, most often the domain name stays the same, whereas the entire URL is changing all the time.
Below are a some examples. The domain name is bold, and what's right-before the domain name is the sub-domain, and what's before that is "http://" which is part of the URL, as described above.
http://kevinbinder.com
http://www.kevinbinder.com
http://about.kevinbinder.com
http:// kevinbinder.com/blog/categories/myOrganization/
http://www.kevinbinder.com/blog/categories/technologyWatch/
http://www.kevinbinder.net
http://kevinbinder.net
.COM vs. .NET
As indicated above, I'm both kevinbinder.com, and kevinbinder.net.
"Why?" you may ask, "did you get both .com, and .net?"
For one, I know there are other Kevin Binder's out there (I got the domain names before some other "Kevin Binder" did). Plus, I wanted to be able to use either .com or .net interchangeably.
More than anything, though, is that to me, kevinbinder.net lends itself better to "Kevin Binder's Network" (of friends, business associates, etc.) than does kevinbinder.com.
.ORG -- Dreamers Unite
Then there's ".org". Perhaps it will always be simply a dream, but I'd really like to be a considerable contribution to humanity and the world. And since I won't be alive forever, and there's a chance that I'll "make it" (perhaps I'll actually have been a substantial contribution to people and the planet), I see kevinbinder.org as the place that could house the "foundation" or legacy I leave behind when my life comes to a close.
So, I'm a dreamer. Why not?
Let the dreamers unite in cyberspace (with weblogs/blogs, web sites, email, and tele-photo-video), by phone, and in person, and let them all have ".org" domain names.
Get your domain names, .COM, .NET, .ORG, .US or otherwise at the lowest possible prices I could find by visiting domains.zaz.com.
Need a Net Coach? Call Kevin JT Binder at 1-877-3BINDER, or visit www.NetCoach.us for a free newsletter, for the Net Coach™ conference call schedule, and for free access to the Net Q & A ™ Library.
|
|
 |
Friday, June 6, 2003 |
Blog is short for weblog.
If you haven't already, you may want to start with What's a Blog? (Part I)
What is a weblog? A weblog is easy to use but less easy to explain . . . Weblogs have a relatively recent but intense history, with implications for web publishing, journalism, and education.
...
A weblog, also called a blog, is a web-based writing space. Think of something like an on-line journal, a website an individual uses to write everyday, where all the writing and editing, and the whole look and feel of the site, is managed through a web browser from wherever the writer happens to be. A weblog is designed so that, just like a journal, the page can be turned each day, and the website itself keeps track of the date and archiving of all the writing.
Like a journal, a weblog is not static, but a dynamic, continually updated site that grows over time with the accumulation of writing and other content.
See the full article: Weblogging: Another Kind of Website by Chris Ashley, written for the fall 2001 edition of Berkeley Computing and Communications
So you want to be a blogger but don't know how to get started? Give me a call: 1-877-3BINDER.
- Kevin JT Binder, Computer Coach
|
|
A Blog is a WebLog. It's an on-line journal.
In fact, the page you're looking at right now is My Blog.
Blog, Blogging, Blogger.
Bog, bogging, booger?
Blogs are a great place to learn about new stuff, a place you can travel the world and get connected, all from the comfort of your own blog.
Blogs are people's news. It's the "Peoples' Newspaper". Blogs make it easy to share your news, and to annotate the news of others.
See more at What's a Blog? (Part II).
Get started. Surf, surf, surf. Enjoy my blog, and the blogs of others. If you're anything like me, you'll be compelled to start your own blog once you get a taste of it.
Give me a call and "try it on". Blogging is so much fun I gaurantee you'll love it, or your money back.
Give me a call and we'll get you started. 1-877-3BINDER
- Kevin JT Binder, Computer Coach
|
|
 |
Thursday, June 5, 2003 |
Everything you want to know, things you didn't know you'd like to know, and more!
Isn't it about time you got caught-up with the times? The computer's here to stay, there's no getting around it. Harness it. Enjoy it. Love it.
My name is Kevin JT Binder. I'll be your coach. Call me toll free 1-877-3BINDER
http://www.computercoach.us
|
|

|
|
|
